Generate Ssh Key Windows 8
How to Generate SSH Public/Private Keys on Windows By Alexandru Andrei – Posted on Sep 17, 2019 Sep 17, 2019 in Windows If you ever managed a Linux server from Windows, you probably used PuTTY or at least heard about it. Sep 26, 2019 On Windows, you can create SSH keys in many ways. If you are using an ssh client on windows to control a remote webserver and want to setup passwordless logins then you need to create ssh keys. The puttygen command from the putty suite can be used to generate keys in both putty and openssh formats. Download the puttygen program from the following url. From PowerShell or cmd, use ssh-keygen to generate some key files. Cd.ssh ssh-keygen This should display something like the following (where 'username' is replaced by your user name) Generating public/private ed25519 key pair. Enter file in which to save the key (C: Users username.ssh ided25519). Ssh-keygen -t rsa -C 'you@example.com' All the rest beginning with line 2 of your script is the output of ssh-keygen. And replace you@example.com with your email address. Have a look at the manual for ssh-keygen to look for additional options. You should probably use a longer key by adding -b 4096 to the option list.
Creating an SSH key on Windows 1. Check for existing SSH keys. You should check for existing SSH keys on your local computer. You can use an existing SSH key with Bitbucket Server if you want, in which case you can go straight to either SSH user keys for personal use or SSH access keys for system use. Open a command prompt, and run. Open up your terminal and type the following command to generate a new SSH key that uses Ed25519 algorithm: Generate SSH key with Ed25519 key type You’ll be asked to enter a passphrase for this. Click on SSH keys and then Add key. Paste the key into the text box: Click Add key. Use SSH keys to connect to Bitbucket Server repositories. SSH access needs to have been set up, as described above. Once this is done, you can use SSH keys as follows: Go to Projects, click a project, and choose a repository from the list.
-->Most authentication in Windows environments is done with a username-password pair.This works well for systems that share a common domain.When working across domains, such as between on-premise and cloud-hosted systems, it becomes vulnerable to brute force intrusions.
By comparison, Linux environments commonly use public-key/private-key pairs to drive authentication which doesn't require the use of guessable passwords.OpenSSH includes tools to help support this, specifically:
- ssh-keygen for generating secure keys
- ssh-agent and ssh-add for securely storing private keys
- scp and sftp to securely copy public key files during initial use of a server
This document provides an overview of how to use these tools on Windows to begin using key authentication with SSH.If you are unfamiliar with SSH key management, we strongly recommend you review NIST document IR 7966 titled 'Security of Interactive and Automated Access Management Using Secure Shell (SSH).'
About key pairs
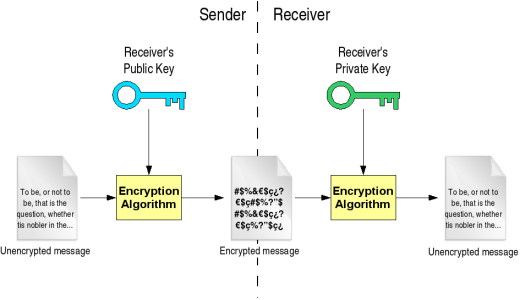
Key pairs refer to the public and private key files that are used by certain authentication protocols.
SSH public-key authentication uses asymmetric cryptographic algorithms to generate two key files – one 'private' and the other 'public'. The private key files are the equivalent of a password, and should stay protected under all circumstances. If someone acquires your private key, they can log in as you to any SSH server you have access to. The public key is what is placed on the SSH server, and may be shared without compromising the private key.
When using key authentication with an SSH server, the SSH server and client compare the public keys for username provided against the private key. If the server-side public key cannot be validated against the client-side private key, authentication fails.
Multi-factor authentication may be implemented with key pairs by requiring that a passphrase be supplied when the key pair is generated (see key generation below).During authentication the user is prompted for the passphrase, which is used along with the presence of the private key on the SSH client to authenticate the user.
Host key generation
Download hp printer 4655 mac. Public keys have specific ACL requirements that, on Windows, equate to only allowing access to administrators and System.To make this easier,
- The OpenSSHUtils PowerShell module has been created to set the key ACLs properly, and should be installed on the server
- On first use of sshd, the key pair for the host will be automatically generated. If ssh-agent is running, the keys will be automatically added to the local store.
To make key authentication easy with an SSH server, run the following commands from an elevated PowerShell prompt:
Since there is no user associated with the sshd service, the host keys are stored under ProgramDatassh.
User key generation
To use key-based authentication, you first need to generate some public/private key pairs for your client.From PowerShell or cmd, use ssh-keygen to generate some key files.
This should display something like the following (where 'username' is replaced by your user name)
You can hit Enter to accept the default, or specify a path where you'd like your keys to be generated.At this point, you'll be prompted to use a passphrase to encrypt your private key files.The passphrase works with the key file to provide 2-factor authentication.For this example, we are leaving the passphrase empty.
Now you have a public/private ED25519 key pair(the .pub files are public keys and the rest are private keys):
Remember that private key files are the equivalent of a password should be protected the same way you protect your password.To help with that, use ssh-agent to securely store the private keys within a Windows security context, associated with your Windows login.To do that, start the ssh-agent service as Administrator and use ssh-add to store the private key.
After completing these steps, whenever a private key is needed for authentication from this client, ssh-agent will automatically retrieve the local private key and pass it to your SSH client.
Note
/pubg-iso-file-for-ppsspp.html. It is strongly recommended that you back up your private key to a secure location,then delete it from the local system, after adding it to ssh-agent.The private key cannot be retrieved from the agent.If you lose access to the private key, you would have to create a new key pairand update the public key on all systems you interact with.
Deploying the public key

To use the user key that was created above, the public key needs to be placed on the server into a text file called authorized_keys under usersusername.ssh.The OpenSSH tools include scp, which is a secure file-transfer utility, to help with this.
Generate Ssh Key Windows Github
To move the contents of your public key (~.sshid_ed25519.pub) into a text file called authorized_keys in ~.ssh on your server/host.
This example uses the Repair-AuthorizedKeyPermissions function in the OpenSSHUtils module which was previously installed on the host in the instructions above.
These steps complete the configuration required to use key-based authentication with SSH on Windows.After this, the user can connect to the sshd host from any client that has the private key.
Generating SSH keys and using them for connecting to SSH servers is a straightforward process on Linux. But for Windows users, Windows does not provide any support for the SSH protocol by default. There is no SSH client that comes by default on Windows. Let alone generating keys.
Let us see how easily we do it on Linux:
Generate Ssh Key Windows Cmd
Key generation in LINUX
You can generate the keys using the ssh-keygen command on the Linux Teminal:
By now, you should have the files id_rsa and id_rsa.pub in the .ssh folder in your home directory. This is how you generate the key pair in linux. The file id_rsa.pub is your public key and id_rsa is your private key. In the public key authentication process with the developed public key you will be able to login to the server. There will be a passwordless authentication process.
Anyway, to save those still using Windows, we have Putty ( http://www.chiark.greenend.org.uk/~sgtatham/putty/ ), the free SSH terminal client, for your connecting needs, and puttygen, for your key generation needs.
Key generation in Windows
The public/private key generation in windows is made possible by a tool called puttygen. With which you can develop the key pair which is required for public key authentication. Here several things are to be noted to avoid problems or errors. The main problem that I faced while trying to login from a windows machine to the server were the 'keys problem'. I have tried a whole lot of things and generated a several set keys as each time I tried to login it shows a different set of errors. In the initial case the error was 'Unable to process the key' and later I realised that the public key generated should be converted to a one-line format. After fixing this error I also tried to have a go. But had come up with a new error message saying that the “Server refused our key”, and later I started to compare the keys generated in a linux machine and a windows machine. And the real solution to the problem has been obtained.
The RSA keys generated in linux machines are of 2048 bits default value and minimum size is 768 bits, whereas the keys generated in windows where 1024 bits. In puttygen there was an option to select the size of the key and it was set as default 1024 bits. In the next problem solving step I changed the default key size value from 1024 to 2048 bits. And thus generated a public/private key pair of 2048 bits size. This time the problem was solved. By setting the auto login user-name, I could login to the system with the public key, no password authentication step was involved.